Hunt down social media accounts with Sherlock

Sherlock is a powerful command line tool that can be used to find usernames across many websites and social networks. It works on Linux, MacOS and Windows.
Installation
To install Sherlock, follow the instructions below. Make sure that you have Python3-pip and Python 3.6 or above installed. You can find Sherlock's github here.
On all platforms
~$ git clone https://github.com/sherlock-project/sherlock.git
~$ cd sherlock
~/sherlock$ pip3 install -r requirements.txt
# On Linux
~$ sudo apt install sherlock
Once installed, you can run Sherlock by python3 sherlock.py -h.
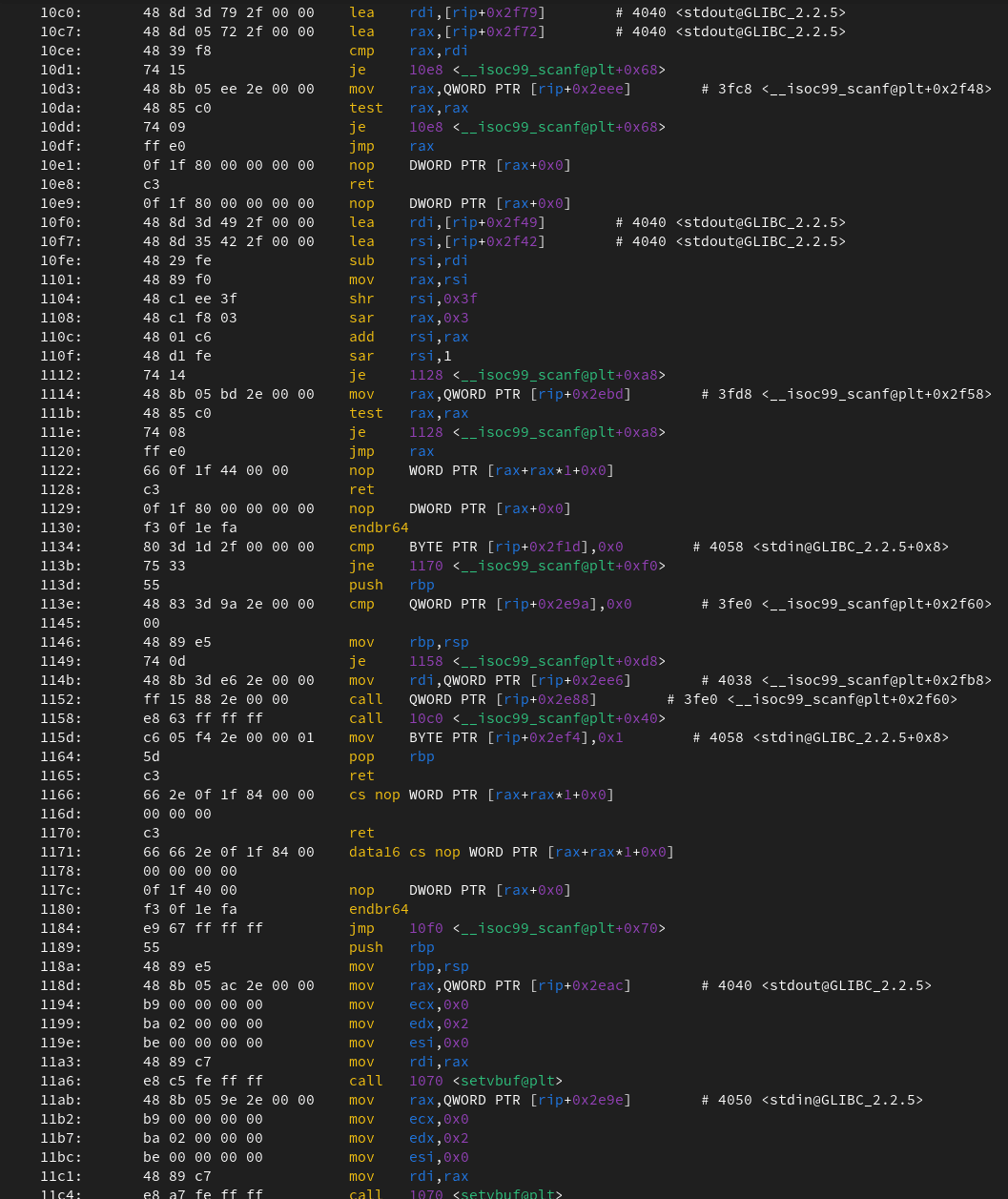
~$ python3 sherlock.py -h
usage: sherlock [-h] [--version] [--verbose] [--folderoutput FOLDEROUTPUT] [--output OUTPUT] [--tor] [--unique-tor] [--csv] [--site SITE_NAME] [--proxy PROXY_URL] [--json JSON_FILE] [--timeout TIMEOUT] [--print-all] [--print-found]
[--no-color] [--browse] [--local]
USERNAMES [USERNAMES ...]
Sherlock: Find Usernames Across Social Networks (Version 0.14.0)
positional arguments:
USERNAMES One or more usernames to check with social networks.
options:
-h, --help show this help message and exit
--version Display version information and dependencies.
--verbose, -v, -d, --debug
Display extra debugging information and metrics.
--folderoutput FOLDEROUTPUT, -fo FOLDEROUTPUT
If using multiple usernames, the output of the results will be saved to this folder.
--output OUTPUT, -o OUTPUT
If using single username, the output of the result will be saved to this file.
--tor, -t Make requests over Tor; increases runtime; requires Tor to be installed and in system path.
--unique-tor, -u Make requests over Tor with new Tor circuit after each request; increases runtime; requires Tor to be installed and in system path.
--csv Create Comma-Separated Values (CSV) File.
--site SITE_NAME Limit analysis to just the listed sites. Add multiple options to specify more than one site.
--proxy PROXY_URL, -p PROXY_URL
Make requests over a proxy. e.g. socks5://127.0.0.1:1080
--json JSON_FILE, -j JSON_FILE
Load data from a JSON file or an online, valid, JSON file.
--timeout TIMEOUT Time (in seconds) to wait for response to requests. Default timeout is infinity. A longer timeout will be more likely to get results from slow sites. On the other hand, this may cause a long delay to gather
all results.
--print-all Output sites where the username was not found.
--print-found Output sites where the username was found.
--no-color Don't color terminal output
--browse, -b Browse to all results on default browser.
--local, -l Force the use of the local data.json file.
You can see that their is many useful options. Notably tor and the proxy flag.
If you installed it using the apt method; all you have to do is type sherlock.
~$ sherlock dingo418
[*] Checking username dingo418 on:
[+] Coil: https://coil.com/u/dingo418
[+] Fiverr: https://www.fiverr.com/dingo418
[+] GitHub: https://www.github.com/dingo418
[+] HackerOne: https://hackerone.com/dingo418
[+] Minecraft: https://api.mojang.com/users/profiles/minecraft/dingo418
[+] PCPartPicker: https://pcpartpicker.com/user/dingo418
[+] Pinterest: https://www.pinterest.com/dingo418/
[+] Scratch: https://scratch.mit.edu/users/dingo418
[+] TikTok: https://tiktok.com/@dingo418
[+] TradingView: https://www.tradingview.com/u/dingo418/
[+] Zhihu: https://www.zhihu.com/people/dingo418
[+] eBay.com: https://www.ebay.com/usr/dingo418
[+] eBay.de: https://www.ebay.de/usr/dingo418
Hunt down accounts
Now all you have to do is choose your target. In this example i have chosen BobSege. The --timeout 10 flag forces Sherlock to skip a website after 10 seconds of no response. I always recommend to add it on.
~$ python3 sherlock.py bobseger --timeout 10
[+] 9GAG: https://www.9gag.com/u/bobseger
[+] Academia.edu: https://independent.academia.edu/bobseger
[+] Apple Developer: https://developer.apple.com/forums/profile/bobseger
[+] Apple Discussions: https://discussions.apple.com/profile/bobseger
[+] Archive.org: https://archive.org/details/@bobseger
[+] AskFM: https://ask.fm/bobseger
[+] Behance: https://www.behance.net/bobseger
[+] Blogger: https://bobseger.blogspot.com
[+] BodyBuilding: https://bodyspace.bodybuilding.com/bobseger
[+] ChaturBate: https://chaturbate.com/bobseger
[+] Clubhouse: https://www.clubhouse.com/@bobseger
[+] Codecademy: https://www.codecademy.com/profiles/bobseger
[+] Coil: https://coil.com/u/bobseger
[+] DailyMotion: https://www.dailymotion.com/bobseger
[+] DeviantART: https://bobseger.deviantart.com
[+] Discogs: https://www.discogs.com/user/bobseger
[+] Disqus: https://disqus.com/bobseger
[+] Docker Hub: https://hub.docker.com/u/bobseger/
[+] Duolingo: https://www.duolingo.com/profile/bobseger
[+] Facebook: https://www.facebook.com/bobseger
[+] Fiverr: https://www.fiverr.com/bobseger
[+] Flipboard: https://flipboard.com/@bobseger
[+] FortniteTracker: https://fortnitetracker.com/profile/all/bobseger
[+] Freesound: https://freesound.org/people/bobseger/
[+] G2G: https://www.g2g.com/bobseger
[+] GaiaOnline: https://www.gaiaonline.com/profiles/bobseger
[+] Genius (Artists): https://genius.com/artists/bobseger
[+] Giphy: https://giphy.com/bobseger
[+] GitHub: https://www.github.com/bobseger
[+] GoodReads: https://www.goodreads.com/bobseger
[+] Gravatar: http://en.gravatar.com/bobseger
[+] Imgur: https://imgur.com/user/bobseger
[+] Instagram: https://www.instagram.com/bobseger
[+] Issuu: https://issuu.com/bobseger
[+] Kik: https://kik.me/bobseger
[+] Kongregate: https://www.kongregate.com/accounts/bobseger
[+] Linktree: https://linktr.ee/bobseger
[+] Minecraft: https://api.mojang.com/users/profiles/minecraft/bobseger
[+] Munzee: https://www.munzee.com/m/bobseger
[+] MyMiniFactory: https://www.myminifactory.com/users/bobseger
[+] Myspace: https://myspace.com/bobseger
[+] Naver: https://blog.naver.com/bobseger
[+] Newgrounds: https://bobseger.newgrounds.com
[+] PCPartPicker: https://pcpartpicker.com/user/bobseger
[+] Periscope: https://www.periscope.tv/bobseger/
[+] Pinterest: https://www.pinterest.com/bobseger/
[+] Pokemon Showdown: https://pokemonshowdown.com/users/bobseger
[+] Pornhub: https://pornhub.com/users/bobseger
[+] Quizlet: https://quizlet.com/bobseger
[+] Rate Your Music: https://rateyourmusic.com/~bobseger
[+] Redbubble: https://www.redbubble.com/people/bobseger
[+] Reddit: https://www.reddit.com/user/bobseger
[+] ReverbNation: https://www.reverbnation.com/bobseger
[+] Roblox: https://www.roblox.com/user.aspx?username=bobseger
[+] Scratch: https://scratch.mit.edu/users/bobseger
[+] Scribd: https://www.scribd.com/bobseger
[+] SlideShare: https://slideshare.net/bobseger
[+] Smule: https://www.smule.com/bobseger
[+] SoundCloud: https://soundcloud.com/bobseger
[+] Telegram: https://t.me/bobseger
[+] Tenor: https://tenor.com/users/bobseger
[+] TikTok: https://tiktok.com/@bobseger
[+] TradingView: https://www.tradingview.com/u/bobseger/
[+] Trello: https://trello.com/bobseger
[+] Twitch: https://www.twitch.tv/bobseger
[+] Twitter: https://twitter.com/bobseger
[+] VSCO: https://vsco.co/bobseger
[+] Wattpad: https://www.wattpad.com/user/bobseger
[+] Wikipedia: https://en.wikipedia.org/wiki/Special:CentralAuth/bobseger?uselang=qqx
[+] WordPress: https://bobseger.wordpress.com/
[+] Xbox Gamertag: https://xboxgamertag.com/search/bobseger
[+] Xvideos: https://xvideos.com/profiles/bobseger
[+] YouNow: https://www.younow.com/bobseger/
[+] YouPorn: https://youporn.com/uservids/bobseger
[+] Zhihu: https://www.zhihu.com/people/bobseger
[+] eBay.com: https://www.ebay.com/usr/bobseger
[+] eBay.de: https://www.ebay.de/usr/bobseger
[+] jeuxvideo: http://www.jeuxvideo.com/profil/bobseger?mode=infos
[+] last.fm: https://last.fm/user/bobseger
[+] mercadolivre: https://www.mercadolivre.com.br/perfil/bobseger
[+] xHamster: https://xhamster.com/users/bobseger
You can find out a lot about your target. In addition, Sherlock also lets you search multiple usernames at once by simply adding a space to your search like below.
~$ python3 sherlock.py dingo dingoo --timeout 10
Useful flags
There is a few other useful flags contained in Sherlock. Here are a couple:
Proxy (-p)
-p allows you to specify a proxy. The proxy has to be in the syntax of -p [TYPE-OF-PROXY]://[IP]:[PORT]. An example is below:
~$ python3 sherlock.py bobseger --timeout 10 -p socks5://127.0.0.1:1080
Tor (-t)
-t allows you to run Sherlock over tor. You will need to be running tor on your current machine and have it added to your system path.
~$ python3 sherlock.py bobseger --timeout 10 -t
Output (-o)
-o allows you to specify an output file for all the positive sites.
~$ python3 sherlock.py dingo418 --timeout 10 -o dingo418.txt
~$ cat dingo418.txt
https://coil.com/u/dingo418
https://www.fiverr.com/dingo418
https://www.github.com/dingo418
https://hackerone.com/dingo418
https://api.mojang.com/users/profiles/minecraft/dingo418
https://pcpartpicker.com/user/dingo418
https://www.pinterest.com/dingo418/
https://scratch.mit.edu/users/dingo418
https://tiktok.com/@dingo418
https://www.tradingview.com/u/dingo418/
https://twitter.com/dingo418
https://www.zhihu.com/people/dingo418
https://www.ebay.com/usr/dingo418
https://www.ebay.de/usr/dingo418
Browser (-b)
-b allows you to automatically open up all the results onto your default browser
~$ python3 sherlock.py bobseger --timeout 10 -b
Ending Notes
Sherlock is a very powerful OSINT tool that is a lot of fun to play around with. You can find a lot about a person
I hope you enjoyed this guide for Sherlock for find social media accounts. If you have any questions you can always leave a comment below or feel free to reach out to me on Twitter @dingo418.