Basic Networking: Internet, IP and MAC Addresses

Today, I am going to start blogging about what is a public and private network, IP Addresses, MAC Addresses. I am going to assume you know a bit about routers, computers and servers.
What is the Internet
When you go to the basics; it is just a bunch of devices connected with a global network of physical cables and a couple of wireless connections. But it is so much more then that. At the base of it is two thing: public and private networks.
What is a network
A network is simply two or more computers that are linked, connected and talk to each other. Some of the common methods that a network can be connected through is a wireless access point, ethernet cable, radio, satelites, etc.
What is a Private Network?
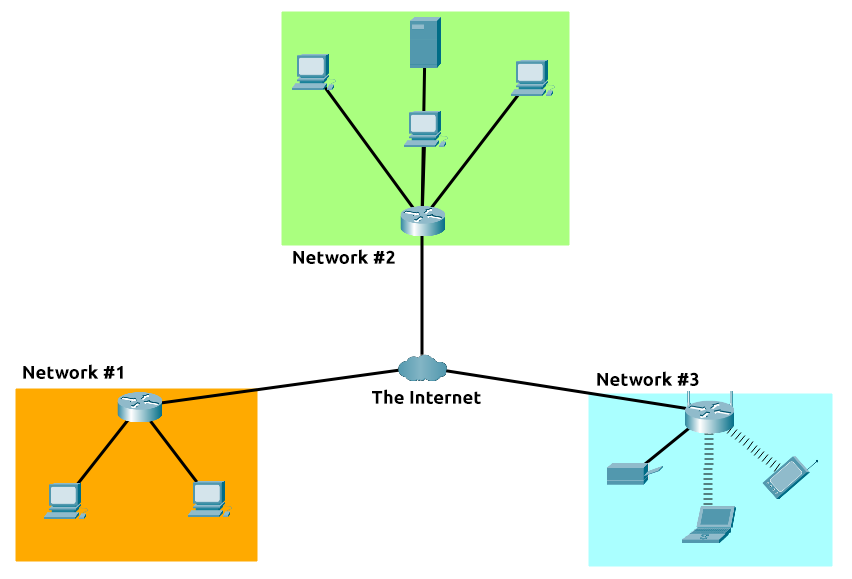
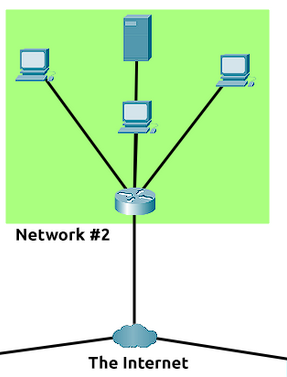
A Private Network is any network that has restrictions established to make a secure environment. This essentially means that very little traffic from outside then network can get in without prior approval. You can see in this diagram that all the machines in the green is in a private network.
What is a Public Network?
A public network is a private network that anybody can connect to. So in this diagram it would be the internet.
Identifying Devices on a Network
Their are mainly two ways to identify machines:
- An IP (or Internet Protocol) Address
- A MAC (Media-Access-Control) Address
IP Addresses
An IP Address is one of the main ways to identify a machine on a network. Their are two types of IP addresses; ipv4 and ipv6. Lets see what an ipv4 looks like bellow:
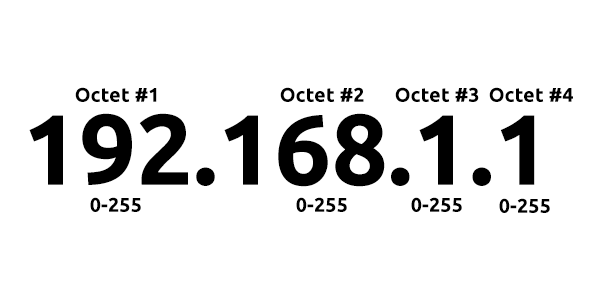
An ipv4 address is separated into 4 octet. The first three octet's are generally a Network ID and the last one is a Host ID. A Network ID tells us where the network belongs to. The Host ID specifies TCP/IP network ie, your network.
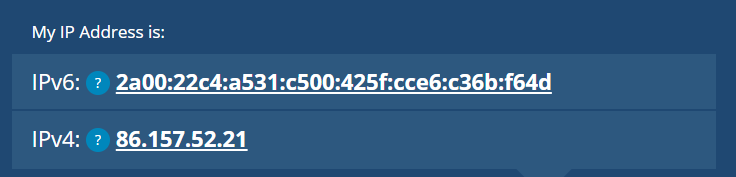
An ipv6 address looks very different compared to an ipv6. Instead of a bunch of numbers it is a lot more letters and number. But why do we have two different IP address? The IPv4 Protocol was made in 1980. Ever since then, the internet has grown rapidly and now their is a shortage of ipv4 addresses. There are only 2^32 IPv4 addresses (4.29 billion). Enough for the 1980s but not with the billions of devices in 2022. Now their is a new protocol for IP addresses that helped resolve this issue, IPv6.
- There is 2^128 IP Addresses (340 trillion-plus)
- As an added bonus they are also more efficient due to new methodologies.
Below is a picture comparing the two of them.
Public vs Private IP Addresses
You have two types of IP Addresses, a public one and a private one. Just like the networks, a private IP is used for all your internal network like messaging another laptop connected to your WiFi or contacting your router. You can give this one away, it has little other use then on your network.
A public IP Address is the thing that all things on the internet contacts you by. An example would be this blog here, or google. This address is automatically assigned to you by your ISP (internet service provider) and is generally dynamic. You have to be a bit more careful with this address as if is put in the wrong hands then they could many things to you like DDoS or finding your general location.
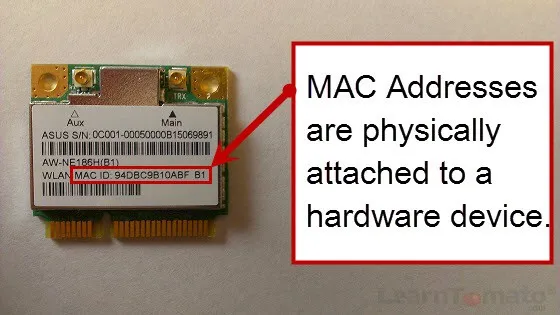
Mac Addresses
A mac address is a 16 digit hexadecmial address in all network cards. Some people call it a physical address as they are generally baked into a network card by the manufacturer. Another good thing to know about MAC addresses is that your ethernet and Wifi card have differnet MAC addresses. Although mac addresses are baked into your network card, It is possible to spoof your MAC address. This can get pass poorly implemented security measures based solely on allowing specfic MAC address through a firewall.
Closing Notes
Next blog post will probably be about how the protocols work. Most of the information is from tryhackme. It is a great website and probably explains it better then me, so go check it out.