What I have learnt from a week of work experience at Kinetic IT

This week, I did work experience for a week at Kinetic IT. I was able to meet many fascinating people and greatly increase my understanding of the cyber security industry. For the week I set myself two main goals.
- Write a blog every day for a week
- Learn as much as possible about the cyber security Industry.
I believe I completed the first goal very well. I have managed to blog every day for a week with high-quality blogs. Although it was tiring; I have managed to learn a lot about the tools for cyber security.
The second goal about learning more about the cyber security industry. I broke the goal up into a couple of smaller goals. They are:
- What kind of jobs are there in the cyber security
- What are the pathways to cyber security.
- What is the work like. For the second goal, I am going to take you threw the highlights of the week from Monday to Friday.
Monday
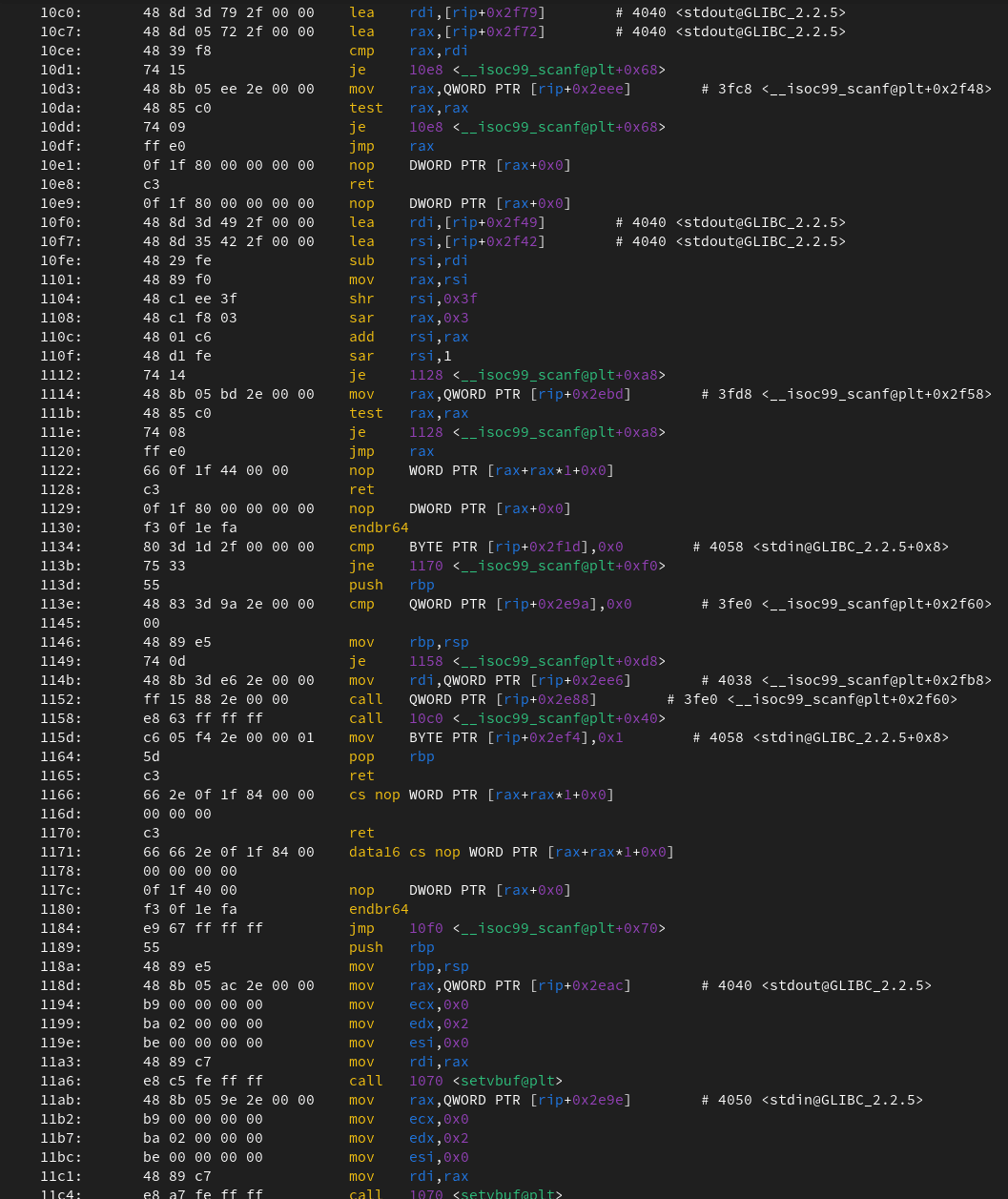
Monday was an exciting day. The first day of work experience! This day mainly contained talking to some Security Operation Centre Analysts. I am not completely sure about who and what I am allowed to talk about, so I apologise if I am a bit vague. But first a bit of background. What is a security Operation Centre Analyst(SOC Analyst)? They are a part of the defence of a system where they combat people trying to hack into a network or system. Using software, such as Logarithm and Microsoft Sentential, machines and servers send Gb's worth of logs to the Security Operation Centre. These systems will then filter out all the useless logs and give the SOC analysts events that are suspicious. If the SOC Analyst looks at events and thinks it is an attack, they will try to mitigate the outbreak as much as possible by shutting down servers and systems to stop the spread. On a general day of working, they will be sifting threw events to see if there is anything suspicious. When they aren't looking at events they will be creating or improving rules to reduce the number of events they are given.
What did we talk about?
I learned a lot about the daily tasks of a SOC analyst. I was able to see how the Microsoft Sentential and LogRhythm worked and some of their detection rules. Sadly, I wasn't allowed to see the tools in action as there was a lot of client confidentiality. In addition, I got to see some of the other services they were working on like their vulnerability bulletin. This is a bulletin that they send out once or twice a week to their clients about recent vulnerabilities or hacker groups.
What did I learn?
I learned a lot from this day as it was my first time learning about SOC Analysts and what they do. I got a feel for what they do and was shown some of the tools they used. I never really considered becoming a SOC Analyst as I never really knew enough about it. But I will consider this in the future.
Tuesday
On the second day, I got the chance to talk to the Director of Security Services at Kinetic IT and another SOC Analysts threw a video call.
What did we talk about? (Director of Security Services)
Talking to the Director of Security Services was incredibly valuable. She talked a lot about how important networks such as LinkedIn are to get jobs. She also said gaining extra qualifications like pentest+ or OSCAP was a must. An important thing that she said that stuck with me is, that if you want somebody else's job, look at their Linkedin and look at what experience and qualifications they have. Then copy them. I was also shown what a report looked like for a penetration test. It was a valuable insight into what they would give the board of a company.
What did I learn?
I learnt the value of Linkedin. Not only showcasing your abilities but being able to gain connections threw LinkedIn is incredibly valuable. I will be making a Linkedin very soon. I will post frequently there. Once I get enough experience I will definitely go for some qualifications like penteast+ or OSCAP.
What did we talk about? (SOC Analysts)
Talking to the other SOC Analysts was a great experience. I was able to talk about their experience on how they became a SOC Analyst. They did not get a University or TAFE degree. They went from working at a computer shop, to a service desk and then to SOC Analysts. One of his main points is that there are many pathways to cyber security. They also talked about what it was like working in the cyber security industry? They essentially said if you do like cyber security it will be very hard to be good at your job. They also suggested some resources to improve my capabilities.
What did I learn?
I learned a couple more resources like Peco CTF or CTFtime.org. I will be creating accounts very soon and start doing more CTFs. I also learned a bit more about the different pathways to cyber.
Wednesday
On Wednesday I had a full corporate induction. This contained everything from health & safety to what KineticIT values are. It was a necessary experience to further understand the industry. The rest of the day I worked through more tryhackme.
Thursday
Thursday was a very quiet day. For most of the day, I continued to work through tryhackme. I learned a bit more general work information from my supervisor Adrian.
Friday
On Friday, I was able to talk to Jess about the careers and paths for cyber security. She also got us to focus on some of the lesser-known jobs in the cyber security industry. She also recommended going to BSides Perth in 2022.
After talking to Jess, The SOC Analysts from Tuesday were available in person. I was able to talk a lot more in-depth with him about cyber.
What did I learn?
When talking to Jess I learned a lot more about the different paths and careers in cyber security.
I talked a bit about everything to SOC Analyst. The talks eventually lead to the process of being in the red team. If you don't know what the red team is; The red team is a team of people that emulate hackers. Depending on the rules of attack; they can physically break into the premise or hack in from the outside. The opposite of the red team is the blue team. The blue team are the defenders from the red team. The monitor logs to see if somebody is trying to hack into the systems. If they detect an intrusion, they will try to contain it as much as possible. The blue team is a much larger team than the red team. What was surprising that I learned is that 90% of the work the red team does, is OSINT investigation. The last 10% is carrying out the hack. OSINT is Open-Source-Inteligence.
Overall
I am very happy with all that I have managed this week. I have been able to wright good quality blogs every day for a week. I also feel like I learned as much as possible about working in the cyber security industry.
Goals
I have learned and reflected a lot on this week but it is no use if I don't set any goals.
My first goal is to learn more about OSINT tools. What surprised me is that 90% of the work of the red team is OSINT. I feel like I must learn these key skills for the future.
My second goal is to continue blogging 1 to 2 a week. I feel like it is an important way of improving my technical writing in addition to forcing myself to learn more material.
My third goal is to complete a CTF once a week. A Capture The Flag is an exercise where a "flag" is found in vulnerable programs. It is a great way to learn more about many different concepts.
My final goal is to continue learning content with Tryhackme once a day. Tryhackme is a great website that teaches you basic to advanced concepts
Goal list:
- Learn more about OSINT tools.
- Continue blogging 1-2 a week
- Do a complete a CTF once a week
- Continue with Tryhackme
Conclussion
Many thanks to KineticIT for allowing me to do work experience there. Thank you to the KineticIT team that warmly welcomed me. They were all happy to chat with me. Special thanks to my supervisor Adrian for setting up and running the week.