Anonymize traffic with Proxychains and Tor on Linux

Whether you want to protect your privacy, run a security test or want to hack the NSA. You want to stay anonymous. This is can be done using a variety of tools like VPNs, proxies and Tor. One of the simplest ways is to use proxychains in conjunction with Tor. It is a simple, secure and free way of staying anonymous. The below guide is for Linux.
What are Proxychains?
Proxychains is a program that redirects our network traffic through multiple servers throughout the world to hide our real IP address. Proxychains link together multiple of these servers together.
What is Tor
Tor is an open-source software used for online privacy and anonymity. It's designed to relay your traffic through multiple relay stations with encryption to hide your true IP address and request. It is not fast and does block some plugins but it is a safe way to browse the web.
Setting it all up
Installing Tor and Proxychains
First up, we need to actually install proxychains and tor with the apt command. It varies on different Linux distributions.
$ sudo apt install tor proxychains4
We now need to start up the tor service.
$ sudo systemctl start tor
If you want to enable it on boot use:
$ sudo systemctl enable tor
You can check if tor is running successfully by:
$ systemctl status tor
● tor.service - Anonymizing overlay network for TCP (multi-instance-master)
Loaded: loaded (/lib/systemd/system/tor.service; disabled; vendor preset: disabled)
Active: active (exited) since Tue 2022-06-14 20:45:12 AWST; 33min ago
Process: 3584 ExecStart=/bin/true (code=exited, status=0/SUCCESS)
Main PID: 3584 (code=exited, status=0/SUCCESS)
CPU: 1ms
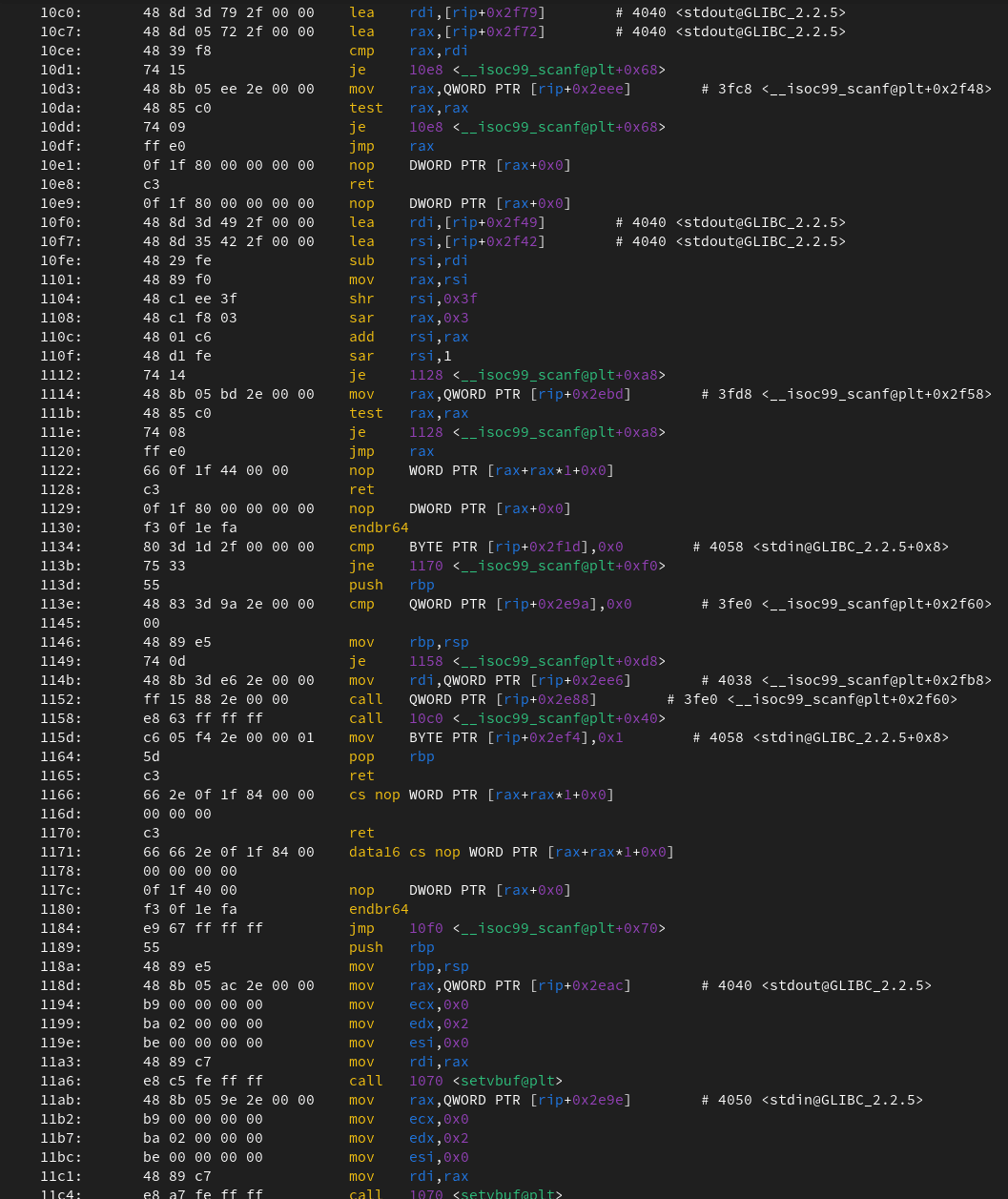
Configuring proxychains:
On most systems, the proxychains configuration file will be located in /etc/proxychains.conf. Sometimes the proxychains.confwill be called proxychains4.conf. If you can still not find the file, use the command locate proxychains.
Now, open up the proxchains.conf in your desired text editor. Firstly, you want to uncomment dynamic_chain and make sure to comment out strict_chain, round_robin_chain, random_chain. This is to balance anonymity with usability.
# proxychains.conf VER 4.x
#
# HTTP, SOCKS4a, SOCKS5 tunneling proxifier with DNS.
# The option below identifies how the ProxyList is treated.
# only one option should be uncommented at time,
# otherwise the last appearing option will be accepted
#
dynamic_chain <--- Uncomment this
#
# Dynamic - Each connection will be done via chained proxies
# all proxies chained in the order as they appear in the list
# at least one proxy must be online to play in chain
# (dead proxies are skipped)
# otherwise EINTR is returned to the app
#
#strict_chain <--- Comment out this
#
# Strict - Each connection will be done via chained proxies
# all proxies chained in the order as they appear in the list
# all proxies must be online to play in chain
# otherwise EINTR is returned to the app
#
#round_robin_chain <--- Comment out this
#
# Round Robin - Each connection will be done via chained proxies
# of chain_len length
# all proxies chained in the order as they appear in the list
# at least one proxy must be online to play in chain
# (dead proxies are skipped).
# the start of the current proxy chain is the proxy after the last
# proxy in the previously invoked proxy chain.
# if the end of the proxy chain is reached while looking for proxies
# start at the beginning again.
# otherwise EINTR is returned to the app
# These semantics are not guaranteed in a multithreaded environment.
#
#random_chain <--- Comment out this
Secondly, uncomment proxy_dns. This is to prevent IP leaks from DNS.
## Proxy DNS requests - no leak for DNS data
# (disable all of the 3 items below to not proxy your DNS requests)
# method 1. this uses the proxychains4 style method to do remote dns:
# a thread is spawned that serves DNS requests and hands down an ip
# assigned from an internal list (via remote_dns_subnet).
# this is the easiest (setup-wise) and fastest method, however on
# systems with buggy libcs and very complex software like webbrowsers
# this might not work and/or cause crashes.
proxy_dns <--- Uncomment this
Finally, add socks5 tor proxy under [ProxyList] like bellow. You can add other proxies for added protection. But remember not all proxies are safe and the more proxies you add, the slower it is going to be. You can find some proxies here.
[ProxyList]
# add proxy here ...
# meanwile
# defaults set to "tor"
socks4 127.0.0.1 9050
socks5 127.0.0.1 9050 <--- add this
<--- you can add other proxies here
Running Proxy Chains
To run firefox through Tor and Proxychains in a firefox private window use this:
proxychains firefox -private https://www.dnsleaktest.com/
Note:
You can run most TCP software through proxychains like nmap, Metasploit, gobuster, etc. All you have to replace is the firefox -private https://www.dnsleaktest.com/ part of the code.
Conclusions
Proxychains and Tor are invaluable resources to know about it. The best part is, it's free! The above configuration balances usability and privacy. Set it up to your own specifications to your desired needs. Some other way to upgrade the security is by making sure you are using HTTPS and TLS. If you want even more protection against snooping eyes, you can use a VPN as well. To do this, use a virtual machine with Proxychains & Tor inside it. You can then route all the traffic going out of the virtual machine with a VPN.
If you want to look at some more resources to learn more:
How TOR Works- Computerphile: https://www.youtube.com/watch?v=QRYzre4bf7I
https://www.linuxfordevices.com/tutorials/linux/proxychains-and-tor
https://hackersonlineclub.com/combination-of-vpn-tor-and-proxychain-for-more-anonymity/