How to crack hashes with John the Ripper

John the Ripper is one of the most loved and versatile hash password-cracking tools out their. It combines speed, ease of use and reliability. But first of what is a hash?
What is a hash?
Hashing is taking a data of any length and turning it into a fixed length string that masks it's original value of the data. Their are hundreds of different hashing algorithms and some of the more common ones are MD5, SHA1, SHA3-512, NTLM, CRC32, etc.
How do you attack hashes?
Their are two over-arching ways of cracking hashes. One of the methods is a rainbow table. Essentially, you have a precomputed table full of hashes that point to the password. This is what most websites like hashes.com use to crack your has. Although it is incredibly fast, it can take a large amount of storage space and can only use "precomputed" hashes. In addition, developers of hashing algorithms have added something called "salt" that changes the hash output. I will not be covering rainbow tables on this blog post.
Then their is the other way. Hashes are designed in a way to make cracking them near impossible. But it is possible to hash a word and see if it matches. This is the method I am going to be using. Although it is not as quick as a rainbow table, it is funner and will be able to crack nearly all hashes.
John the Ripper
Installation of John the Ripper
You can install John the ripper on your respective systems by using this link. To use john use the syntax bellow:
# Linux
john hash.txt
#Windows
./john.exe hash.txt
The Modes of John the Ripper
Single Crack Mode
This mode makes use of the information already available inside the username. The format for text file is:
username:hash
Some examples of how this would work would be with the word Anonymous:
Anonymous
an0nym0us
AnOnYmOuS
Anonymous1
Syntax: This mode is the default mode the JtR starts with but you can specify it with:
john --single hash.txt
Wordlist Crack Mode
In this mode it computes the hashes of a word list and then compares it to the one given. In JtR you can use any specified word list but it does choose a default one if none is specified. For this post i am going to be using the infamous rockyou wordlist. Example Usage:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=raw-md5 crack.txt
Incremental Crack Mode
Incremental mode is the most powerful cracking mode. It tries every single possible combination of characters until it completes. This means it will not stop. Example usage:
john --incremental hash.txt
You can specify the option for the incremental mode by:
john --incremental=digits incremental.txt
john --incremental=Alpha incremental.txt
You can see all the options in the john.conf in /etc/john/john.conf
.
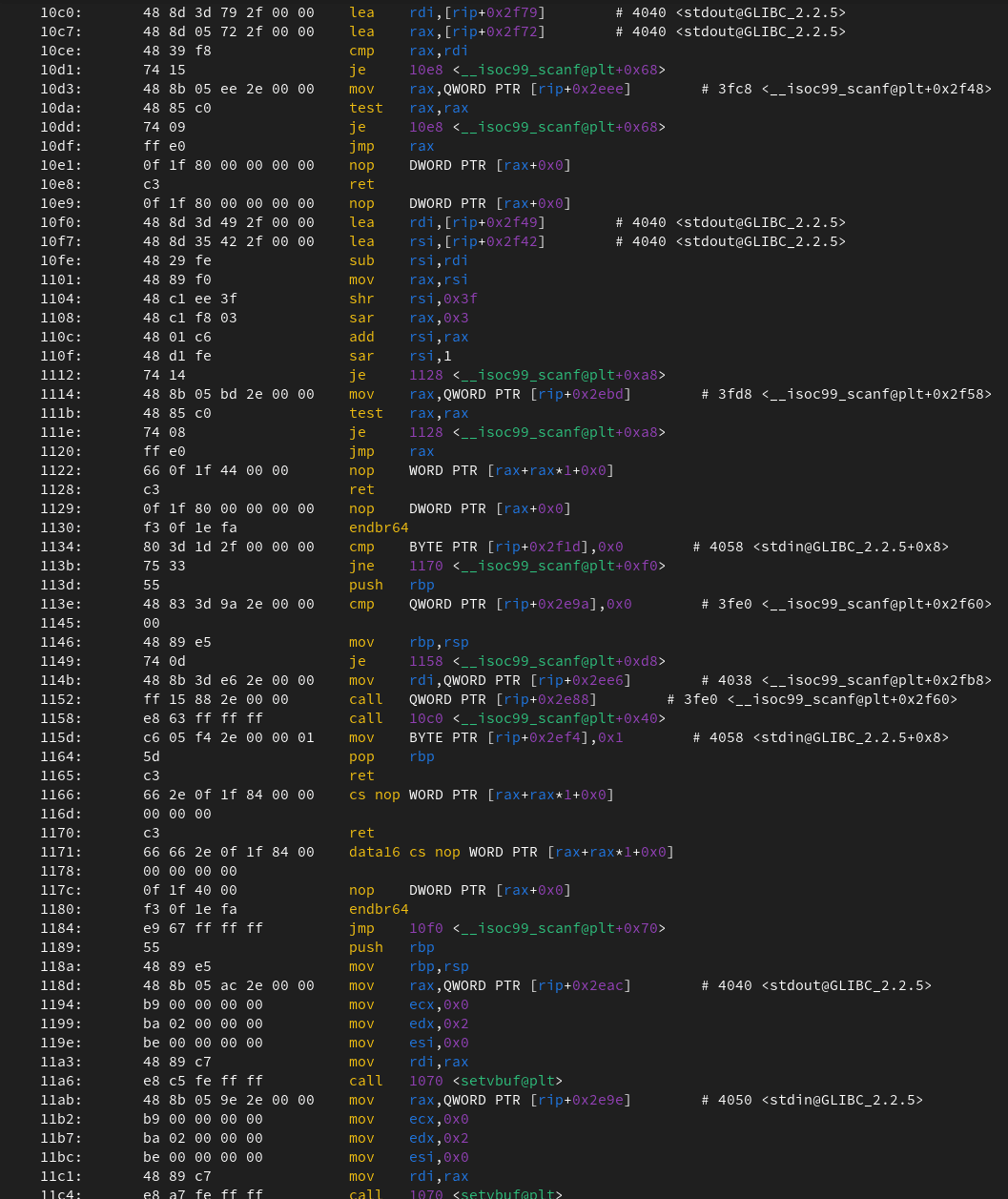
Identifying hashes
John's auto hash detection can be a bit unreliable. Here, is a good script for identifying hashes in python.
Format-specific Cracking
john --format=[format] [path to file]
--format= - Input the format of the hash
Example Usage:
john --format=raw-md5 --wordlist=/usr/share/wordlists/rockyou.txt hash_to_crack.txt
Notes:
If you are unsure about telling John which hash type to crack, use john --list=formats. If you are search for a specific type of hash use john --list=formats | grep -iF "md5", if you are on Linux.
Cracking Multiple files
To crack multiple files that have the same encryption just add them both to the end. The syntax for multiple md5 hashes is as so: john [file 1][file 2]
john -form=raw-md5 crack.txt md5.txt
Cracking other files
Sometimes the hash is not easy to extract from a file. That is when Jumbo John comes in handy. It has a bunch of different tools for extracting hashes out of other formats. I will cover a few here.
Zip2John
We are going to use zip2john to output a hash in a text file. This can then be attacked like a normal hash.
zip2john [options] [zip file] > [output file]
Example Usage:
zip2john zipfile.zip > zip_hash.txt
Rar2John
Almost identical to the zip2john tool, we can output a RAR file to a hash text file. John will be able to understand this.
rar2john [rar file] > [output file]
Example Usage:
rar2john rarfile.rar > rar_hash.txt
SSH2John
You know, I wonder if their is a pattern to this? You can find your pub id_rsa private key in linux at ~/. ssh/id_rsa
ssh2john [id_rsa private key file] > [output file]
Example Usage:
ssh2john id_rsa > id_rsa_hash.txt
Practise
If you want to practice some hash cracking, here are some hashes.
Sources
https://tryhackme.com/room/johntheripper0
https://www.hackingarticles.in/beginner-guide-john-the-ripper-part-1/
https://www.varonis.com/blog/john-the-ripper
Documentation
https://www.openwall.com/john/doc/
https://github.com/openwall/john